What is natural language generation?
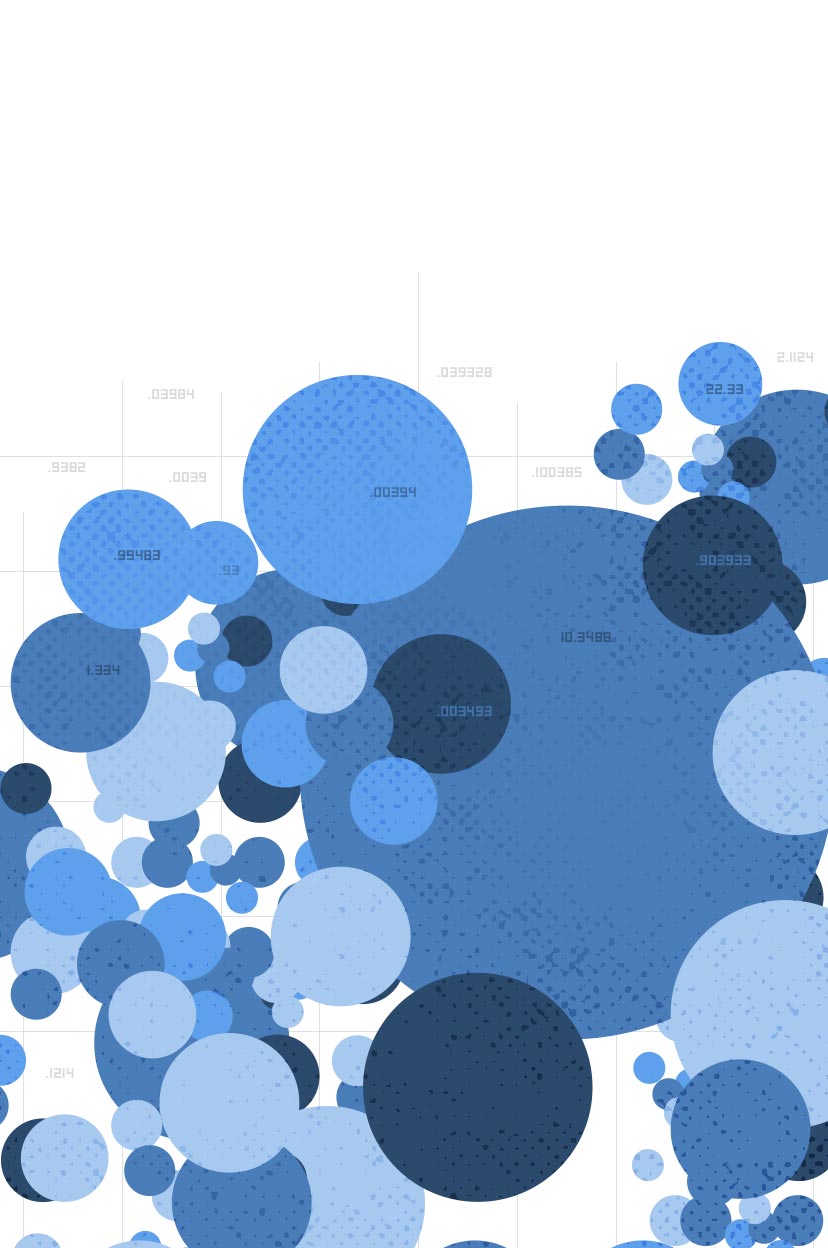
Natural language generation (NLG) is a technology that transforms data into clear, human-sounding narratives—for any industry and application.
Natural language generation (NLG) is a technology that transforms data into clear, human-sounding narratives—for any industry and application.










Wehkamp uses Wordsmith to automate the product descriptions and listings for over 300,000 unique products.

There’s no way Allstate could produce what we’re doing today having analysts spend time manually writing reports. We thought Wordsmith was a novel idea and wanted to jump on it.

We couldn’t be happier. When you look at the 170-year history of a company like the Associated Press, part of its success has been adapting and innovating in new media formats. . . We see this as part of that history.